Your Linux system is more than just a machine it is a gateway to your personal data work environment and digital identity. With cyber threat growing every year even the most stable and secure operating systems need an additional layer of protection. Whether you’re running Linux on a home computer a server or a development workstation implementing basic hardening steps can dramatically reduce risks and keep your environment safe.
Linux is known for its robust architecture but security doesn’t come from the system alone. It comes from how you configure it how you manage user access, and how you maintain it over time. Simple mistakes like leaving unused services open or giving excessive privileges to users can become entry points for attackers. The good news is that with the right practices, you can shield your system from most common vulnerabilities.
Strengthening your Linux machine. You will discover how to manage users responsibly control what runs on your system and apply practical hardening techniques that create a safer and more resilient environment. Every step is designed to be actionable easy to follow, and suitable for personal or professional use.
Introduction to Linux System Security and Hardening
Securing a Linux system begins long before an issue appears. Even though Linux is widely recognized for its stability and strong security model no operating system is fully protected by default. The real strength lies in how you configure it, how you manage access, and how you maintain it over time. Hardening is the process of reducing vulnerabilities limiting unnecessary exposure and ensuring your system follows safe practices from the ground up.
A well secured Linux machine does not just protect your data it also ensures consistent performance reliability and peace of mind. Whether you are a system administrator a developer or a regular user trying to make your computer safer learning the basics of Linux hardening help you build a strong foundation against modern threats.

Why Linux System Security Matters
Linux powers everything from personal laptops to enterprise server cloud platforms and embedded devices. Because of its wide usage it becomes an attractive target for cybercriminals. Most attacks happen not due to flaws in Linux itself but because of weak configurations or poor access control.
A secure Linux system helps you:
- Protect sensitive data from unauthorized access
- Prevent misuse of system resources
- Avoid downtime and performance issues caused by malicious activity
- Build trust in the systems you manage
- Comply with best practices expected in professional environments
What Is System Hardening?
System hardening refers to intentionally reducing the attack surface of your system. This mean removing unnecessary components tightening configurations, and ensuring only trusted users and services can operate on your machine.
Hardening is not a one time task it is an ongoing process that evolves as your system grows.
Keypoints of Linux Hardening
- Disable unused services to prevent unwanted access
- Keep software updated with security patches
- Limit user privileges and use the principle of least access
- Strengthen authentication methods such as passwords and permissions
- Monitor system logs to detect unusual activity
- Use firewall rules to control incoming and outgoing traffic
The Role of User Management in Security
User accounts play a major role in the overall safety of a Linux environment. Poorly managed account with excessive permissions can expose the entire system to unnecessary risk. Proper user management ensures each individual receives only the access they need nothing more.
Effective user management includes:
- Creating user accounts with the right privileges
- Removing or disabling old or unused accounts
- Managing groups to organize permissions
- Applying strict password policies
- Tracking account activity for abnormalities
When these practices come together they create a strong defense that makes it significantly harder for unauthorized users to exploit your system.
Understanding Basic Linux Security Principles
Strengthening a Linux system starts with understanding the core security principles that guide its design. Linux was not built with security as an afterthought it incorporates a layered model that controls how users processes and files interact. These foundational concepts help ensure that even when something goess wrong the system can limit the damage and maintain stability.
Whether you are managing a personal laptop or a production server knowing these basics will help you make smarter decisions and build a stronger security posture.

The Principle of Least Privilege
One of the most important ideas in Linux security is that every user and process should have only the permissions necessary to do their job. Nothing more.
Prevent accidental damage unauthorized actions or misuse of system resources.
Keypoints:
- Grant minimum required access
- Avoid using the root account for everyday tasks
- Use
sudoresponsibly and sparingly - Limit the installation of tools or services that require elevated privileges
User and Group Separation
Linux is built around a structured permission model where every file and directory belongs to a user and a group. This structure is not just organizational it is a core security mechanism.
Keypoints:
- Assign users to groups based on their actual roles
- Restrict sensitive directories to specific groups
- Review group memberships regularly
- Avoid mixing administrative and regular tasks within the same account
File and Directory Permissions
Linux permissions determine who can read write or execute a file. These rules help protect system files from being modified or accessed by unauthorized users.
Permissions are your first line of defense especially on multi user systems.
Keypoints:
- Regularly check permissions using
ls -l - Avoid giving write permission to “others”
- Restrict access to configuration files
- Ensure scripts and executables are only available to trusted users
Authentication and Password Policies
Strong authentication helps prevent unauthorized access to your system. Passwords remain the primary method of login for many Linux environments so their strength plays a crucial role.
Keypoints:
- Use long complex passwords
- Enforce regular password updates if necessary
- Disable password-based login for unused accounts
- Encourage the use of secure authentication methods like SSH keys
Service and Process Control
Every running service increases the potential attack surface of your system. Managing services carefully helps reduce unnecessary exposure and improves system efficiency.
Keypoints:
- Disable or remove unused software
- Review active services with tools like
systemctl - Keep only essential network-facing services running
- Monitor background processes for suspicious behavior
Regular Updates and Patch Management
Even stable systems require updates to remain secure. Software vulnerabilities are discovered all the time and updates provide patches that close these risks before attackers can take advantage.
Keypoints:
- Apply security updates promptly
- Enable automatic updates if appropriate
- Keep both the kernel and installed packages current
- Remove outdated or unsupported applications
These principles helps you build a secure foundation for your Linux system. Each of these concepts works together to minimize risks improve system integrity, and protect your environment from common threats.
Implementing User Management Best Practices
User management is one of the most powerful security controls in Linux. A well structured user system ensures that every person or process interacting with the machine has clearly defined permissions and responsibilities. Poor user management on the other hand, can create unnecessary risks from unauthorized access to accidental system modifications. When you implement these strong user management practice you build a stable and controlled environment where each action is traceable and correctly authorized.
Linux gives you precise control over users groups permissions and access levels. Your task is to use those tools wisely to maintain a secure and well organized system.
Create Users with Purpose, Not Convenience
A common mistake is using one shared account for multiple people or tasks. This removes accountability and makes it impossible to identify who made what changes. Each user should have their own account even if they only need temporary access.
Creating accounts with purpose ensures clarity tracking and easy removal when access is no longer needed.
Key insights:
- Separate personal users administrative users and service accounts
- Avoid shared accounts because they hide activity and complicate audits
- Assign descriptive usernames that reflect responsibilities
- Remove or lock accounts immediately when no longer required
Use Groups to Organize Permissions Smartly
Groups help you avoid giving individual users unnecessary access. Instead of manually assigning permissions to each user, you place them in groups that define what they can do.
For example: developers might belong to a “dev” group with access to code directories while system administrators belong to a group with elevated privileges.
Key insights:
- Create groups based on roles, not individuals
- Review group memberships regularly to avoid privilege creep
- Keep administrative groups small and trusted
- Avoid mixing staff roles within the same group
Limit Administrative Access with Sudo
Administrative privileges are powerful and should be tightly controlled. Linux handles this through the sudo command. which allows temporary access to elevated tasks without logging in as the root user.
Ensures changes are logged intentional, and less prone to accidental damage.
Key insights:
- Avoid logging in directly as root use sudo instead
- Grant sudo access only to users who truly need it
- Log all sudo actions for auditing and accountability
- Customize sudo rules to restrict specific commands if necessary
Use Strong Password Rules and Account Policies
Passwords still remain a crucial part of Linux authentication and weak passwords create serious vulnerabilities. Strong policies help ensure that users adopt secure practices reducing the risk of unauthorized login attempts.
Linux allows you to enforce password aging strength requirements and account lockouts to protect your system further.
Key insights:
- Enforce minimum password length and complexity
- Require regular password updates if your environment demands it
- Lock accounts after repeated failed login attempts
- Disable password login for accounts that rely on SSH keys only
Manage Shell Access Properly
Not every user needs shell access. Many accounts especially system or service accounts should only exist to run specific processe not to log in or execute commands.
Carefully controlling shell access reduces the risk of misuse and keeps your environment stable.
Key insights:
- Assign
/bin/falseor/usr/sbin/nologinto accounts that should not log in - Avoid giving shell access to automated or service related accounts
- Monitor which users have valid shells and remove unused ones
Monitor User Activity and Access Logs
User management doesn’t end after creating accounts it requires ongoing monitoring. Logs help you understand who accessed the system what commands were run and whether anything unusual happened.
Proactive monitoring allows you to spot suspicious behavior before it becomes a serious problem.
Key insights:
- Regularly review
/var/log/auth.logor similar authentication logs - Track failed login attempts and identify patterns
- Monitor sudo logs for sensitive actions
- Use log monitoring tools to automate alerts for suspicious activity
Regularly Audit and Clean Up Accounts
Over the time systems accumulate old accounts from former staff unused service accounts or temporary access sessions. These inactive accounts become weak points if left unattended.
Routine audits help you maintain a clean and secure user environment.
Key insights:
- Remove or disable accounts that are no longer active
- Clean up unused groups and outdated permissions
- Verify that service accounts are still linked to active services
- Review access levels periodically to ensure they still match roles
Securing the Linux Kernel and System Services
The Linux kernel is the core of your operating system and every action performed on your machine passes through it. A secure kernel protects your system from stability issues unauthorized actions and performance problems. When combined with strong control over system services it becomes the foundation of a reliable and resilient environment.
Strengthening the kernel and securing system services does not require advanced experience. It simply requires consistent upkeep attention to configuration details and proper management of the components that keep the system running.
Keeping the Kernel Updated for Maximum Protection
Kernel updates are not just about new features. They include performance improvements – bug fixes and security patches that close vulnerabilities discovered by developers. Running an outdated kernel increases the risk of system exploitation and compatibility problems.
Updating your kernel ensures that your operating system is equipped with the latest safeguards and improvements.
Key insights–
• Always install security patches soon after they become available
• Enable update notifications to stay informed about new releases
• Remove old kernels only after confirming that the new one works correctly
• Use stable and trusted repositories for kernel updates
Managing System Services to Reduce Exposure
Every active service consumes resources and could become a potential entry point if improperly configured. Reviewing which services are running, you can remove unnecessary ones and secure the ones you rely on.
Key insights–
• Review all active services using appropriate Linux tools
• Disable services that are not essential to your workflow
• Keep service configuration files protected and accessible only to trusted users
• Use minimal service sets on servers to reduce overall exposure
Applying Access Control to Critical System Files
Kernel settings and system service configurations are usually stored in protected directories. These files must remain secure because unauthorized modifications can cause serious system instability. Proper access control ensures that only trusted administrators have permission to modify these essential components.
Strong file protection helps maintain system integrity and reliability.
Key insights
• Keep kernel configuration files readable only to privileged users
• Restrict modification permissions to prevent accidental or harmful changes
• Monitor changes to system directories that contain service configuration files
• Regularly validate permission settings to ensure they meet security standards
Using Built In Security Modules for Extra Protection
Linux offers security modules that extend kernel protection and enhance access control. These modules act as an additional filter that approves or denies system actions based on predefined rules. They help prevent unauthorized programs or users from performing actions that could harm the system.

Using these modules strengthens your environment without requiring drastic changes.
Key insights–
• Enable security modules that fit your environment needs
• Review module rules to ensure they support your security policy
• Use logging features to track actions blocked by the module
• Combine module protection with other security measures for best results
Ensuring System Services Start in a Controlled State
Many Linux services rely on startup settings that determine how and when they activate. If these settings are not managed correctly unnecessary services may run unexpectedly. Setting up a controlled startup process prevents confusion, reduces load on the system, and strengthens overall security.
Well managed startup services maintain a cleaner and safer environment.
Key insights
• Review which services start automatically during boot
• Allow only trusted and essential services to run at startup
• Monitor boot logs to identify slow or problematic services
• Remove startup entries for software that you no longer use
Monitoring Kernel and Service Logs for Early Warnings
Logs provide important insight into how your system behaves. They reveal issues such as repeated errors, unauthorized access attempts or malfunctioning services. Monitoring logs regularly helps you detect problems early before they grow into serious incidents.
Consistent log analysis is one of the most reliable ways to ensure long term security.
Key insights
• Review kernel logs for unusual activity or errors
• Track service logs to identify performance or security issues
• Set up alerts for repeated failures or suspicious patterns
• Store and rotate logs properly to prevent loss of valuable information
Enhancing Authentication Methods for Stronger Security
Strengthening authentication is one of the most important steps in building a secure Linux environment. Authentication determines who can access the system and what level of control they have once inside. When authentication methods are weak attackers have a much easier path to misuse accounts bypass restrictions or compromise sensitive resources. Strong and layered authentication ensures that only trusted users can enter the system and that access attempts are verified with reliable security measures.
Strong authentication is not only about choosing long passwords. It involves understanding how Linux handles login methods managing account policies implementing secure keys and removing unnecessary authentication pathways. With the right configuration, you can dramatically reduce unauthorized access and maintain a trustworthy system.

Using Strong and Well Structured Password Policies
Passwords remain one of the most widely used authentication methods in Linux. Weak or predictable passwords leave the system vulnerable to brute force attempts. A secure password policy ensures that users choose combinations that are difficult to guess and resistant to common attack techniques.
Linux allows administrators to enforce rules on password length – complexity and expiration. These policies encourage users to maintain good habits and prevent shortcuts that can weaken security.
Key insights
• Require longer passwords with a mix of letters numbers and symbols
• Enforce expiration rules only when necessary for organizational policy
• Block simple patterns and dictionary based passwords
• Educate users to avoid password reuse across systems
Using SSH Keys for Safer Remote Access
SSH keys provide a highly secure method for authenticating remote logins. Unlike passwords keys cannot be easily guessed copied or brute forced. They rely on cryptographic pairs that authenticate identity with far greater strength.
Using SSH keys is one of the best ways to protect remote servers because it eliminates the need for password based login and significantly reduces the risk of unauthorized access.
Key insights
• Generate keys locally and keep the private key protected
• Disable password authentication when SSH keys are used
• Store keys in secure locations with proper access permissions
• Use passphrases on keys for additional protection
Restricting Root Login for Safer System Access
Direct root login is a significant security risk because it removes accountability and provides full system control without limitation. Restricting root login ensures that administrators use sudo for privilege elevation which keeps actions logged and provides an additional layer of review.
Linux systems benefit greatly from removing or minimizing direct root access because it prevents accidental system wide damage and stops unauthorized users from exploiting open pathways.
Key insights
• Disable remote root login completely
• Use sudo to perform administrative tasks with proper logging
• Limit root access to a very small number of trusted users
• Require strong authentication whenever root privileges are needed
Enabling Account Lockout and Rate Limiting
Every failed login attempt provides information to someone trying to guess credentials. If the system allows unlimited attempts, attackers can continue without restriction. Account lockout policies stop repeated attempts by temporarily blocking access after several failures.
Rate limiting works alongside lockout rules by reducing the number of attempts allowed within a specific timeframe. Together, they significantly reduce brute force risks.
Key insights
• Lock accounts after a set number of failed attempts
• Apply reasonable cooldown periods to slow repeated guesses
• Record failed login attempts for auditing
• Combine lockout rules with strong passwords for better protection
Managing Inactive Accounts Carefully
Inactive user accounts become silent vulnerabilities on Linux systems. Old account might still have valid credentials outdated passwords, or unnecessary access rights. Properly managing inactive accounts prevents unauthorized use and keeps the authentication system clean.
Regular audits help ensure that only active and legitimate users have access to the system.
Key insights
• Disable accounts that are no longer needed
• Remove unnecessary login shells from unused accounts
• Regularly verify if service accounts are still in use
• Clean up leftover accounts after staff or project changes
Implementing Multi Factor Authentication for Additional Assurance
Multi factor authentication adds a second layer of verification making it much harder for unauthorized users to access the system. Even if a password is compromised the additional verification step blocks entry.
Linux systems can integrate MFA for critical accounts remote access or administrative tasks to strengthen security significantly.
Key insights
• Use MFA for administrative and remote access accounts
• Combine MFA methods with SSH keys for even stronger protection
• Store MFA recovery codes securely
• Apply MFA selectively to avoid unnecessary complexity
Regular Maintenance and Monitoring for Ongoing Security
Maintaining a secure Linux system is not a one time task. Security must be treated as a continuous process because threats evolve software changes, and system configurations grow over time. Regular maintenance ensures that your system stay healthys while monitoring helps you detect unusual behavior before it becomes a problem. A well managed system is far more resilient and performs better because issues are addressed early rather than after damage is done.
Ongoing security is built through consistent updates log review system cleanup & performance checks and careful observation of the system behaviors. When these practices become part of your routine you create a stable and trustworthy environment that stays secure even as new challenges emerge.
Keeping Your System Updated Without Delays
Updates are essential because they provide security patche performance fixes and improvement that protect your Linux installation from known vulnerabilities. Delaying updates leaves your system exposed to issues that developers have already solved. Applying updates regularly ensures your environment stays aligned with the latest security standards.
Updates should be checked frequently and installed responsibly to maintain uninterrupted operation.
Key insights
• Review available updates on a consistent schedule
• Apply security patches as soon as they are released
• Verify update logs to confirm successful installation
• Remove unsupported or outdated software to reduce risk
Monitoring Logs for Early Warning Signs
Logs are the system way of telling you what is happening behind the scenes. They record authentication attempts service behavior errors warning and unusual activities. Regularly monitoring logs gives you early insight into potential issues.
Checking logs allows you to detect suspicious login attempts failing services or misconfigurations long before they cause damage.
Key insights
• Review authentication logs for login failures and irregular patterns
• Monitor system logs to track errors and operational issues
• Use tools that notify you when unusual events occur
• Keep logs organized and rotate them to prevent storage problems
Cleaning Up Unused Files and Accounts
Over the time system gather leftover files outdated accounts unnecessary packages and temporary data. These forgotten items can create clutter and potential risks. Cleaning them up helps maintain a smooth and secure system.
Removing what you do not need ensures that no hidden vulnerabilities are left behind and that your system performs efficiently.
Key insights
• Delete inactive user accounts that no longer serve a purpose
• Remove temporary files and old system logs
• Uninstall unused software that adds unnecessary bloat
• Review directories that accumulate leftover or cached items
Checking System Performance to Detect Abnormal Behavior
Performance issues often appear before security problems are fully visible. A sudden spike in CPU usage unexpected memory consumption or unusual processes may signal unauthorized activity or failing services. Observing performance helps you recognize these abnormalities early.
Regular system checks keep you aware of how your machine normally behaves and alert you when something seems off.
Key insights
• Monitor CPU – memory and disk usage regularly
• Investigate unknown or suspicious processes immediately
• Review network activity for unexpected traffic
• Maintain a baseline of normal system performance for comparison
Backing Up Important Data on a Consistent Schedule
Backups are essential for protecting against data loss corruption or system failures. Even the most secure system can experience unexpected problems, and backups ensure you can restore critical information without stress.
A reliable backup strategy protects your files and provides peace of mind especially during updates or configuration changes.
Key insights
• Create backups of important files and system configurations
• Store backups in secure and separate locations
• Test backup files to confirm they restore correctly
• Schedule automated backups for consistency
Regularly Reviewing Security Settings and Policies
Security settings can become outdated as your system evolves or as new features are added. Reviewing your settings ensures they still match your needs and follow current best practices.
A periodic review helps you identify weak areas and adjust configurations before they cause vulnerabilities.
Key insights
• Reevaluate user permissions and group memberships
• Check firewall rules and adjust them when necessary
• Review authentication policies for gaps or outdated rules
• Update security guidelines to reflect system changes
Conclusion
Securing a Linux system is an ongoing process that combines careful planning consistent maintenance and informed user management. The core principles of Linux security managing user accounts responsibly hardening system services strengthening authentication and monitoring your system regularly you build a reliable and resilient environment.
Security is not achieved through a single step or tool but through a layered approach where every measure reinforces the others. A well hardened Linux system protects sensitive data ensures smooth performance and gives you peace of mind knowing that your system is prepared to resist potential threats.
FAQs
Q1. What is Linux system hardening?
Linux system hardening is the process of reducing vulnerabilities by securing configurations, managing users, limiting services, and applying best practices to protect the system.
Q2. How can I secure Linux user accounts?
Use strong passwords, implement sudo for administrative tasks, organize users into groups, disable inactive accounts, and monitor activity regularly.
Q3. Are SSH keys safer than passwords for Linux login?
Yes, SSH keys provide cryptographic authentication that is harder to guess or brute force compared to traditional passwords.
Q4. How often should I update my Linux system?
Security updates should be applied as soon as they are available, while regular maintenance updates can be scheduled weekly or monthly depending on the system’s role.
Q5. What is the role of monitoring in Linux security?
Monitoring logs and system performance helps detect suspicious behavior early, identify misconfigurations, and ensure ongoing protection against potential threats.

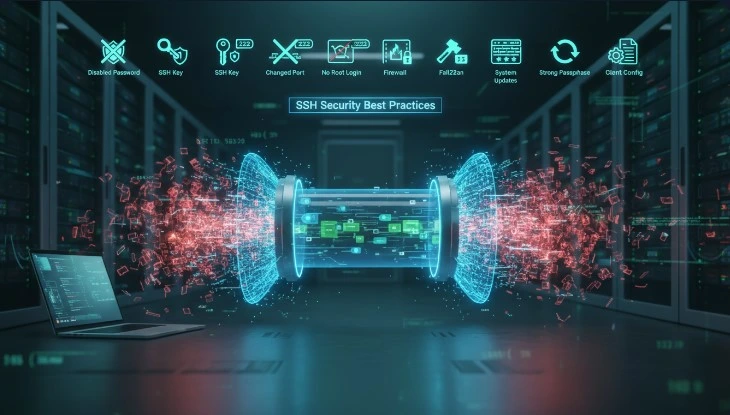
Pingback: SSH Security Best Practices for Secure Remote Access in Linux - OS Insight Wiki