Two-Factor Authentication: Enhancing Account Security Without Passwords
Two factor authentication add an extra shield to your account by requiring a second verification step beyond your password. Even if someone gets your login details they cannot access your account without this additional code or confirmation. With modern authentication methods like biometrics verification apps and push notifications 2FA makes your online accounts far more secure often without needing traditional passwords at all.
Introduction to Two-Factor Authentication (2FA)
Two Factor Authentication also known as 2FA is a strong security method that protects your online accounts with more than just a simple password. Many people think a password alone keeps their data safe but this is not true at all. Threat actors can guess weak passwords or steal them through different tricks like phishing or keylogging. This is why 2FA became a needed layer of protection for every user.
What Makes 2FA Important
2FA gives you an extra step that confirms your identity before access is allowed. Even if someone gets your password they cant enter your account without the second proof. This reduces the chance of hacking by a big level. It also makes users feel more safe while using banking apps email services social media platforms and more.
How 2FA Works
The system works by asking for two different types of verification
One thing you know which is your password
One thing you have like a code sent to your phone or a security app
One thing you are like your fingerprint or face scan
Using two of these factors at the same time creates a strong shield against unauthorized access.
Types of 2FA Methods
SMS Based Codes send a short code to your phone to verify login but can be intercepted.
Authenticator Apps generate time-based codes on your device and work even offline making them more secure.
Biometric Verification uses fingerprints face scan or voice to confirm identity and is hard to replicate.
Hardware Security Keys are physical devices that must be tapped or inserted to access accounts offering the strongest protection.
- SMS Based Codes
- You get a shorts code on your mobile phone. This is the most common method but sometimes not the safest because messages can be intercepted.
- Authenticator Apps
- Apps like Google Authenticator or Microsoft Authenticator generate time based codes. These apps are more secure and work even without internet.
- Biometric Verification
- This include fingerprint scan face scan or voice recognition. Biometric checks are fast and very difficult for attacker to copy.
- Hardware Security Keys
- Physical USB or NFC keys give the strongest level of protection. You must plug or tap the device to verify your login.
Why Users Should Enable 2FA
2FA protects your identity your private info and your digital assets. It provides a strong safeguard against unauthorized access attempt. It is not hard to set up and most platforms already support it for free. With online threats growing every year activating 2FA is no longer optional. It is a must for everyone who wants safer digital life.
The Role of Two-Factor Authentication in Modern Security
Two Factor Authentication now plays a very big role in modern digital security because passwords alone are no longer enough to stop attacker. Online threat grow every single day and hackers use smarter tools to break into accounts. 2FA adds a second shield that stops most of these attacks and keeps users safe even when their password is leaked or stolen.
How 2FA Strengthens Security
Modern cyber attacks often target weak passwords reused passwords or stolen credentials. With 2FA the attacker cant move further because they still need the second verification step. This extra layer blocks unauthorized access and makes your account way harder to compromise.
Protection Against Common Cyber Attacks
- Phishing Attacks
- Even if someone tricks you into sharing your password they still fail to enter your account since they dont have the second factor.
- Credential Stuffing
- Thread actor use leaked passwords from other sites to try and break into your accounts. 2FA stops these attempts instantly.
- Brute Force Attacks
- Attackers try thousands of password guesses in hope of finding the right one. 2FA makes this type of attack useless.
Why 2FA Is Needed Today
People store more private details online than ever before like photos financial data work files and identity info. Without strong security this data can be stolen or misused. 2FA gives users a simple but powerful way to protect everything they keep online.
2FA in Business and Professional Environments
Companies also depend on 2FA to stop unauthorized access to sensitive systems. It helps protect employee accounts cloud storage tools and company networks. Many businesses now make 2FA mandatory because it reduces data breaches and saves huge loss.
A Reliable Defense for the Future
As digital risks continue to rise 2FA stands as one of the simplest and most effective defenses. It is easy to enable free to use on most platforms and trusted by security experts worldwide. Anyones who cares about safe online activity should use it as a basic layer of protection.
Key Benefits of Implementing Two-Factor Authentication
Two Factor Authentication gives users and organizations a strong advantage in protecting their digital account and sensitive information. Many people still rely on passwords alone but 2FA makes accounts much harder to hacks. It add extra layers of protection that prevent unauthorized access and gives peace of mind to users.
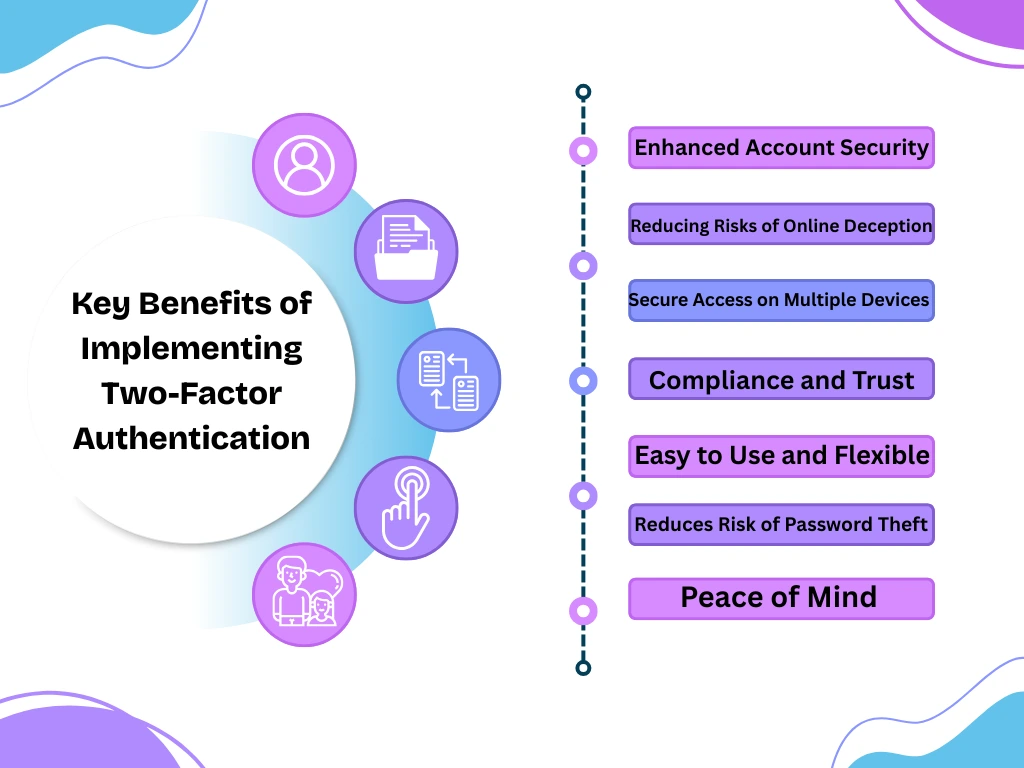
Enhanced Account Security
2FA protects accounts from hackers even if your password is stolen. Without the second factor attackers cannot enter your account. This reduces the risk of identity theft data breaches and financial loss significantly.
Reducing Risks of Online Deception
Phishing attack try to trick users into sharing passwords but 2FA blocks these attempts. Even if you enter your password on a fake site the hacker cant access your account without the second verification step.
Secure Access on Multiple Devices
Many people access their accounts from phones laptops and tablets. 2FA ensures that every login on any device is verified. This prevents unauthorized logins and keeps all devices safe.
Compliance and Trust
Businesses that use 2FA meet security standards and compliance rules. Customers trust companies more when they see accounts are protected with extra security measures.
Easy to Use and Flexible
2FA methods like apps push notifications SMS codes and biometrics are easy to use. Users can choose the method that fits their needs. Setup is fast and most platforms support it without extra cost.
Reduces Risk of Password Theft
Even if someone guesses or steals your password they still cant access your account. This makes password leaks much less dangerous and lowers chances of data loss.
Peace of Mind
Knowing your accounts are protected with 2FA makes users feel safer. Personal information financial accounts and work files stay secure from threat actor.
How Two-Factor Authentication Works Without Relying on Passwords
Two Factor Authentication can work even without using traditional passwords. this is called passwordless authentication and it is becoming very popular in modern security systems. Instead of typing a password users relys on other verification methods to prove their identity and gain access to accounts.
Passwordless Methods
Biometric Verification
Users can use fingerprint face scan or iris scan to log in. The system recognizes unique biological features that are nearly impossible to replicate by threat actor.
One-Time Codes via Apps or Devices
Some systems send a code to your phone or an authenticator app. You just enter the code to verify yourselfs and no password is required.
Push Notifications
Instead of passwords the service sends a login request to your device. You just need approve it and gain access instantly.
Hardware Security Keys
Physical devices like USB or NFC keys allow login by tapping or inserting the device. This will be completely removes the need for a password and gives strong protection.
Advantages of Passwordless 2FA
- Reduces the risk of stolen or weak passwords
- Makes login faster and simpler for users
- Protects accounts against phishing attack because no password is entered
- Works across multiple devices without remembering complex passwords
How It Improves Security
Without the password there is nothing for attackers to steal or gues. Even if your device is lost the second factor or biometrics verification stops unauthorized access. It combines convenience and security in a way traditional password cannot matchs.
Overcoming Common Two-Factor Authentication Challenges
Two Factor Authentication is very useful but sometimes users face challenges while using it. Knowing these problem and how to overcome them can make 2FA easier and more effective for everyone.
Lost or Stolen Devices
Many 2FA methods rely on phones or hardware keys. If a device is lost it can lock you out of your accounts. To overcome this users should keep backup codes in a safe place. Some services also allow multiple devices to be registered so you can still login if one device is missing.
App or Code Not Working
Authenticator apps sometimes fail or codes dont generate. The solution is to check the time settings on your device and keep the app updated. Using backup methods like SMS codes or alternative apps can also help in emergencies.
User Resistance
Some people find 2FA annoying or complicated. Educating users about the benefits and showing how easy it is to use can solve this problem. Simple methods like push notifications or biometrics make adoption faster.
Compatibility Issues
Not all websites or services support every type of 2FA. Choosing widely supported methods like authenticator apps or SMS codes can reduce this issue. Busines should also ensure their systems are compatible with multiple 2FA options.
Recovery Options
Having recovery options is important if you cant access your second factor. Backup codes recovery emails or support from the service provider ensures you dont get locked out permanently.
Balancing Security and Convenience
Sometimes users feel security slows them down. Using smart methods like passwordless login or biometric verification keeps security high without making the process too long or difficult.
The Future of Two-Factor Authentication and Passwordless Security
the future of online security is moving fast and Two Factor Authentication is at the center of this changes. Passwords alone are becoming less reliable as threat actor find smarter ways to steal them. Passwordless security combined with 2FA is the next big step in protecting accounts and digital information.
Trends in 2FA Technology
Biometric Everywhere
Future systems will rely more on fingerprints face scan and voice recognition. Biometrics are fast accurate and very hard to duplicate making accounts safer than ever.
Passwordless Login
Many platforms are removing passwords completely. Users just approve login requests or use biometrics to enter accounts. It make online life simpler and safer at the same time.
Hardware Security Keys Expansion
More companies will adopt physical keys that protect sensitive systems. These keys are almost impossible to threat and will become standard in business security.
AI Assisted Security
Artificial intelligence can detects un usual login attempts and trigger 2FA automatically. This adds an extra layer of protection without bothering the user every time.
Benefits for Users and Organizations
- Safer online experience with less risk of stolen credentials
- Faster login without remembering complex passwords
- Reduced risk of phishing attacks and account takeover
- Better trust for businesses and customers
How to Set Up Two-Factor Authentication for Your Accounts
Setting up the two factor authentications is easies than most people think and it can make your accounts much safer, Almost all the major platform and services support 2FA so you can enable it on your email social media banking and cloud accounts.
Step 1 Choose Your 2FA Method
Decide which method works best for you.
You can use..
- Authenticator apps like Google Authenticator or Microsoft Authenticator
- SMS codes sent to your phone
- Push notifications on your device
- Biometric login using fingerprint or face recognition
- Hardware security keys like USB or NFC devices
Step 2 Enable 2FA in Account Settings
go to your account security settings and look for Two Factor Authentication or 2FA. Most platforms give you clear steps to activate it. follow the instructions and select your preferred method.
Step 3 Register Your Device
If you use an app or biometric method you may need to register your device. This links the device to your account so you can verify logins easily.
Step 4 Save Backup Codes
Most services provide backup codes in case your device is lost or unavailable. Save these codes somewhere safe but accessible. It ensure you dont get locked out of your account.
Step 5 Test Your 2FA
Try logging in from a different device or browser to make sure 2FA works correctly. Enter the second verification method and confirm you can access your account.
Step 6 Keep 2FA Updated
If you change your phone or security device make sure to update your 2FA settings. This prevents accidental lockouts and keeps your account secures at all times.
Tips for Easy Use
- Use an authenticator app for higher security than SMS
- Keep backup codes offline
- Enable multiple verification methods if possible
- Educate family members or employees if it is a shared account
Setting up theTwo Factor Authentication may take few minutes but it makes your digital life much safer. Once active you can relax knowing your accounts are protected from most attacks.
Conclusion:
The Two Factor Authentication is one of the simplest and most effective ways to protect your online accounts. Passwords alone are no longer enough to keep hackers out. Adding a second verification step blocks unauthorized access and keeps your personal and professional data safe.
authenticator apps push notifications biometrics or hardware keys you can secure accounts without making login too hard. Even passwordless systems now provide strong protection while improving convenience.
Enabling the2FA reduces the risk of phishing attack password theft and unauthorized logins. It is easy to set up and supported by almost every major platform. For businesses it also improves trust and helps meet security compliance.
FAQs
Q1. What is Two-Factor Authentication (2FA)?
Two-Factor Authentication is a security method that adds a second verification step to protect your accounts beyond just a password.
Q2. How does 2FA improve account security?
It blocks unauthorized access even if your password is stolen by requiring a second factor like a code, biometric, or security key.
Q3. Can I use 2FA without a password?
Yes, modern 2FA supports passwordless login using biometrics, authenticator apps, push notifications, or hardware keys.
Q4. Which 2FA method is the safest?
Hardware security keys and authenticator apps are considered the most secure because they are hard for hackers to bypass.
Q5. How do I set up Two-Factor Authentication?
Go to your account security settings, choose a 2FA method, register your device, save backup codes, and test it to make sure it works.



2 Comments